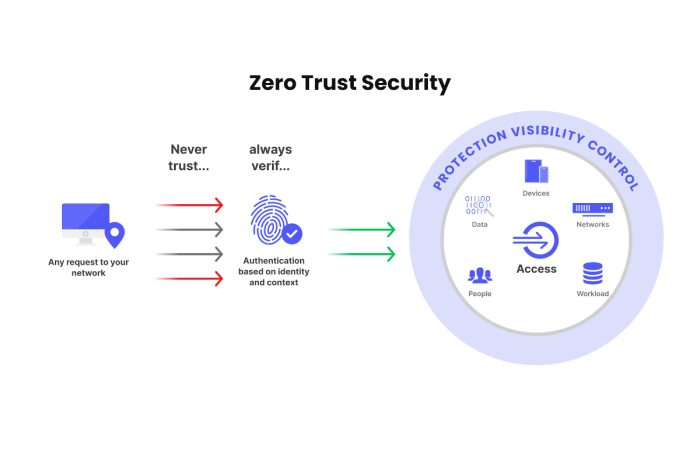
Traditional perimeter-based security assumes that users or devices inside the network are trustworthy. That assumption no longer holds. Hybrid work, SaaS adoption, cloud workloads, and identity-based attacks have made internal networks as vulnerable as external ones.
The Zero Trust model removes implicit trust. Every user, device, and application must continuously prove its legitimacy before accessing resources.
The concept is widely formalized by the National Institute of Standards and Technology through Zero Trust Architecture (ZTA) guidance such as NIST SP 800-207 Zero Trust Architecture. According to the model, security should rely on continuous verification, least-privilege access, and granular segmentation rather than perimeter defenses.
For organizations in 2026, zero trust is no longer theoretical. It is becoming a baseline architecture for cloud-first infrastructure.
This guide provides:
- A 20-point Zero Trust security checklist
- Architecture patterns for SMBs and enterprises
- Vendor categories and tools
- A step-by-step migration strategy
- Compliance considerations and executive communication templates
Table of Contents
Core Principles of Zero Trust
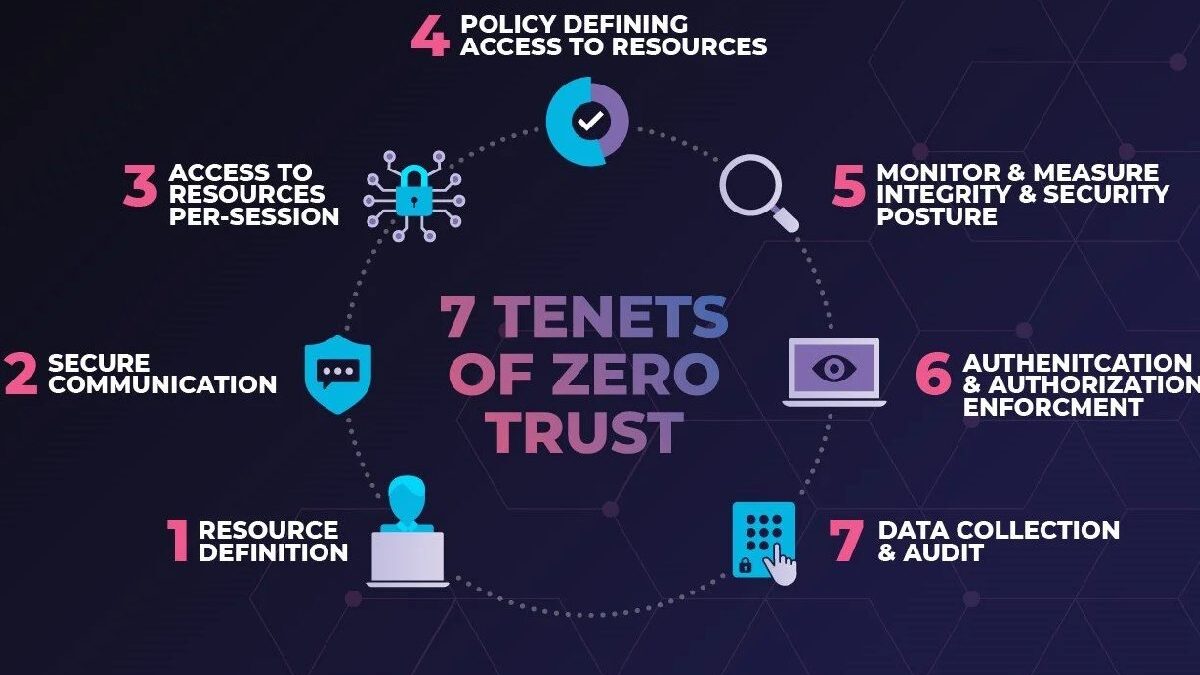
Before implementation, it is important to understand the three operational pillars behind Zero Trust Architecture.
- Verify Explicitly
Every access request must be authenticated and authorized using multiple signals:
- Identity credentials
- Device posture
- Network location
- Behavioral context
- Risk scoring
Authentication becomes continuous, not just a login event.
- Enforce Least Privilege
Users and systems should only receive the minimum access required to perform tasks.
Techniques include:
- Just-in-time access
- Role-based access control
- Attribute-based policies
- Privileged access management
Least privilege significantly reduces the blast radius of breaches.
- Assume Breach
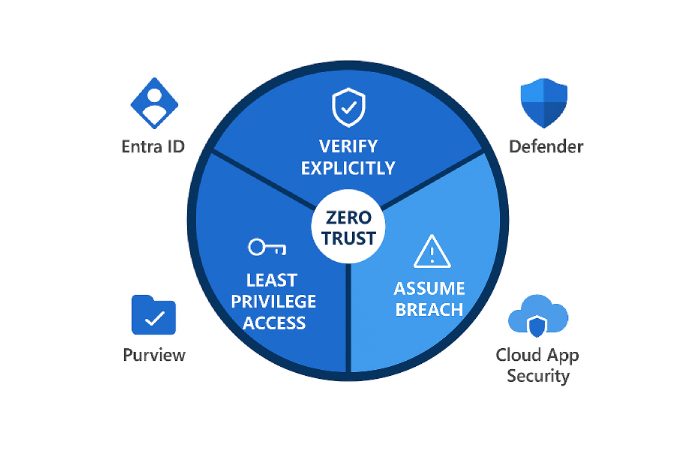
Zero trust assumes attackers may already be inside the network.
Therefore organizations must:
- Segment networks
- Monitor activity continuously
- Detect anomalies quickly
- Automate containment
The 20-Point Zero Trust Security Checklist
The following checklist provides a practical implementation baseline.
Identity and Access Management
- Enforce Multi-Factor Authentication (MFA)
All users, administrators, and external partners should authenticate using MFA. - Deploy Identity Federation or Single Sign-On (SSO)
Centralize identity management through an IDaaS platform. - Implement Role-Based Access Control (RBAC)
Map access permissions to roles rather than individuals. - Apply Just-in-Time Privileged Access
Privileged roles should only activate temporarily when needed. - Use Risk-Based Conditional Access
Evaluate login risk based on behavior, device, and location.
Device Security
- Verify Device Posture Before Access
Ensure devices meet compliance requirements such as:
- Updated OS
- Disk encryption
- Endpoint protection
- Enforce Device Registration
Corporate devices should be enrolled in device management systems.
- Block Unmanaged Devices
Restrict or sandbox access for unknown devices.
- Deploy Endpoint Detection & Response (EDR)
EDR tools provide behavioral detection and threat telemetry.
Network Architecture
- Implement Microsegmentation
Divide networks into small logical segments to isolate workloads.
- Replace VPN-Centric Access with ZTNA
Zero Trust Network Access provides application-level access instead of network-level connectivity.
- Apply Software-Defined Perimeters
Applications remain invisible until authenticated users request access.
- Encrypt Internal Traffic
Use TLS or equivalent encryption even for internal communications.
Application Security
- Adopt Strong API Authentication
Use OAuth tokens, certificates, or identity-aware proxies.
- Integrate Application Security Testing
DevSecOps pipelines should include:
- SAST
- DAST
- Dependency scanning
- Protect Workloads with Runtime Monitoring
Container security and runtime anomaly detection improve application visibility.
Monitoring and Telemetry
- Centralize Security Logs
Aggregate logs from identity systems, endpoints, and cloud infrastructure.
- Use Security Information and Event Management (SIEM)
SIEM tools correlate activity across the environment.
- Deploy User and Entity Behavior Analytics (UEBA)
UEBA detects unusual patterns indicating compromised accounts.
- Automate Incident Response
Security orchestration tools can isolate devices or revoke access instantly. (Zscaler)
Example Zero Trust Architectures
Implementation differs depending on organization size and infrastructure maturity.
SMB Architecture
Small and mid-size organizations typically rely on cloud-native security services.
Typical components
- Identity provider (SSO + MFA)
- Endpoint security agent
- ZTNA gateway
- Cloud security monitoring
Access flow:
- User authenticates via SSO
- Device posture verified
- ZTNA broker validates policy
- Application access granted
Advantages:
- Lower infrastructure complexity
- Faster deployment
- Reduced maintenance
Enterprise Architecture
Large organizations usually integrate zero trust into existing infrastructure.
Key components include:
- Enterprise identity federation
- Privileged access management
- Microsegmentation platforms
- Security analytics platforms
- Cloud security posture management
Enterprise architecture often includes:
- Multiple identity providers
- Hybrid cloud infrastructure
- Advanced behavioral analytics
The complexity requires phased deployment and automation.
Zero Trust Vendor Categories (Tool Matrix)
Organizations usually combine tools across several security categories.
| Category | Purpose | Example Vendors |
| Identity & Access (IDaaS) | Authentication, SSO, MFA | Okta, Microsoft, Ping Identity |
| Endpoint Protection / EDR | Device monitoring and threat detection | CrowdStrike, SentinelOne |
| SASE / ZTNA | Secure remote application access | Zscaler, Cloudflare |
| Microsegmentation | Isolate workloads and servers | Illumio, VMware |
| SIEM / Analytics | Log correlation and threat detection | Splunk, IBM |
The right combination depends on cloud maturity, workforce size, and regulatory requirements. (National Institute of Standards and Technology)
Zero Trust Migration Plan (Pilot → Scale)
Organizations should treat zero trust as a multi-phase transformation rather than a one-time deployment.
Phase 1 — Assessment
Tasks:
- Inventory users, devices, and applications
- Identify critical data flows
- Map existing authentication systems
- Assess risk exposure
Deliverable: Zero Trust readiness assessment report
Phase 2 — Pilot Implementation
Start with a limited environment.
Common pilot targets:
- Remote workforce access
- A critical SaaS application
- Developer infrastructure
Goals:
- Test policy enforcement
- Measure user experience impact
- Validate security telemetry
Phase 3 — Policy Expansion
Gradually extend:
- Identity verification
- Device compliance rules
- Application segmentation
At this stage organizations often introduce behavioral analytics.
Phase 4 — Automation and Scale
Mature zero trust environments rely heavily on automation.
Examples:
- Automated device quarantine
- Identity risk scoring
- Policy orchestration across cloud services
Automation reduces operational overhead while maintaining security.
Compliance and Audit Considerations
Zero trust supports multiple regulatory frameworks.
Examples include:
| Compliance Standard | Relevance |
| NIST Cybersecurity Framework | Security risk management baseline |
| General Data Protection Regulation | Strong identity and data access controls |
| Health Insurance Portability and Accountability Act | Patient data protection |
| Payment Card Industry Data Security Standard | Cardholder data protection |
Because zero trust provides granular logging and policy enforcement, it simplifies compliance audits.
Auditors can easily trace:
- Access approvals
- Authentication events
- Data movement
Executive Communication Template
Security leaders often need executive buy-in before launching zero trust initiatives.
Below is a simplified internal message structure.
Subject
Proposal: Zero Trust Security ImplementationProposal: Zero Trust Security Implementation
Hi Team,
As our organization continues expanding cloud services and remote access, our current perimeter-based security model is becoming less effective.
I recommend that we begin adopting a Zero Trust Architecture aligned with the latest guidance from NIST. This model removes implicit trust from our network and requires verification for every user, device, and application request.
Benefits include:
- Reduced risk of lateral movement during breaches
• Stronger protection for sensitive data
• Better visibility into user activity and device health
• Improved compliance readiness
I propose launching a pilot program focused on remote access and SaaS applications. After evaluating performance and security metrics, we can expand the architecture across additional systems.
I will share a detailed implementation roadmap and cost estimates in the upcoming security strategy meeting.
Best regards
Security Team
Frequently Asked Questions
Is Zero Trust only for large enterprises?
No. Many SMBs implement simplified zero trust architectures using cloud identity providers and ZTNA services.
Does Zero Trust eliminate VPNs?
Not necessarily. Many organizations still use VPNs but gradually transition to application-level access models.
How long does implementation take?
Typical timelines:
- SMB environments: 3–6 months
- Enterprise environments: 12–24 months
The duration depends on infrastructure complexity and organizational readiness.
Is Zero Trust expensive?
Costs vary depending on tooling. However, many organizations already own components such as identity management, endpoint security, and SIEM platforms.
The primary investment is architecture integration and policy development.
Conclusion
Zero Trust is rapidly becoming the dominant model for enterprise cybersecurity. Instead of relying on a network perimeter, organizations must validate every user, device, and workload continuously.
Following a structured checklist helps transform the concept into a practical implementation roadmap. By prioritizing identity verification, device posture validation, network segmentation, and continuous monitoring, organizations can significantly reduce breach impact and improve operational visibility.
The most effective strategy is to start small—pilot identity-driven access controls, validate policies, and then gradually expand across the environment. With careful planning and the right tool ecosystem, Zero Trust Architecture can evolve into a resilient security foundation for modern cloud-first organizations.