Mysk2 Dyndns Org Mysk2 – Has been growing in importance as users connecta to various systems their home servers, NAS appliances, private networks or surveillance systems via internet-accessible infrastructure. Dynamic DNS services like DynDNS enable users to remain reachable despite frequently-shifting internet IP addresses.
With the continued worldwide growth of solutions for remote working, cloud storages, intelligent-household facilities and many other solutions, network further facilitates almost ubiquitous access and becomes more important for people and enterprises. Dynamic DNS providers usually focus on:
- remote desktop access
- NAS connectivity
- home automation systems
- IP camera monitoring
- personal server hosting
Mysk2.dyndns.org seems to be an address of a remote-access host or an endpoint in connecti0n with the DynDNS Port-Forward domain connected to a Dynamic DNS account, which is most often used as a host of a home-server or a free-access system.
Rather than behaving like a traditional public website, such domains often function as network-access points tied to private infrastructure.
This article explains:
- what Dynamic DNS is
- how DynDNS infrastructure works
- why users search domains like mysk2.dyndns.org
- remote networking concepts
- cybersecurity risks and protections
- the future of remote-access systems
Table of Contents
What Is Mysk2 Dyndns Org Mysk2 Switzerland?
The keyword “mysk2.dyndns.org mysk2” appears to be associated with a Dynamic DNS endpoint rather than a normal commercial website.
Possible Networking Role
Dynamic DNS domains are often linked to:
- home servers
- remote-access gateways
- NAS devices
- camera systems
- personal networking infrastructure
The “dyndns.org” component strongly suggests use of Dynamic DNS services.
Why It Looks Different From Normal Websites
Traditional websites usually rely on:
- fixed hosting infrastructure
- static server environments
- dedicated web services
Dynamic DNS domains often behave differently because they may point to:
- changing residential IP addresses
- temporary network endpoints
- remote-access systems
This distinction is important for understanding search intent.
Switzerland Relevance
The Switzerland geographic modifier may indicate:
- user location relevance
- server-hosting region
- traffic association
- regional networking usage
However, Dynamic DNS endpoints can technically be accessed globally depending on configuration.
What Is Dynamic DNS (DynDNS)?
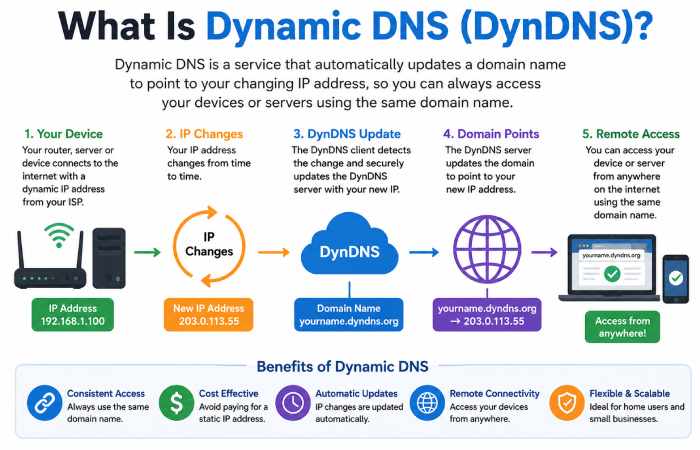
Dynamic DNS (DDNS) is a networking system that allows internet-connected devices to remain accessible even when their public IP address changes.
Why IP Changes Matter
Most residential internet connections use:
- dynamic IP addresses
- periodically changing network assignments
This creates challenges for:
- remote access
- persistent connectivity
- external device communication
Without Dynamic DNS, users would constantly need to track changing IP addresses manually.
How DynDNS Solves the Problem
Dynamic DNS services automatically update DNS records whenever an IP address changes.
This allows users to access systems through:
- consistent domain names
- stable remote endpoints
- easier network management
instead of memorising changing IP addresses.
Why DynDNS Became Popular
Dynamic DNS became widely used because it simplified:
- remote networking
- personal server hosting
- internet-connected surveillance
- NAS accessibility
It remains important in many networking environments today.
How Dynamic DNS Services Work
IP Address Changes
Internet service providers often assign:
- temporary public IPs
- rotating residential addresses
When these addresses change, external connectivity can break.
Dynamic DNS services monitor these changes automatically.
Domain Mapping Systems
DynDNS platforms map:
- changing IP addresses
to: - persistent domain names
For example:
- a changing residential IP
can remain reachable through: - mysk2.dyndns.org
This creates continuous accessibility.
Remote Access Configuration
Dynamic DNS systems commonly support:
- remote desktop access
- NAS systems
- surveillance devices
- smart-home infrastructure
Users configure routers or software clients to update DNS records automatically.
Continuous Network Availability
The main advantage is persistence.
Users no longer need to:
- check changing IPs manually
- reconfigure remote connections constantly
The Dynamic DNS provider manages endpoint mapping automatically.
Common Uses of DynDNS Infrastructure
Dynamic DNS supports many modern networking scenarios.
Home Servers
Users often host:
- personal websites
- media servers
- file systems
- gaming servers
from residential internet connections.
NAS Remote Access
Network Attached Storage (NAS) devices frequently use Dynamic DNS for:
- remote file access
- backup retrieval
- cloud-style personal storage
Security Camera Systems
Remote surveillance access commonly relies on:
- Dynamic DNS endpoints
- internet-accessible camera systems
- mobile monitoring applications
Gaming Servers
Some hobbyists use Dynamic DNS to host:
- multiplayer game servers
- community gaming infrastructure
Remote Desktop Connectivity
Users may remotely access:
- work computers
- personal systems
- private networks
through secure remote-access configurations.
Why Users Search Domains Like Mysk2 Dyndns Org
Search behaviour around unusual domains often reflects technical curiosity or security concerns.
Security Verification
Users commonly search unfamiliar domains to determine:
- legitimacy
- safety
- ownership context
- possible risks
Network Troubleshooting
Technical users may investigate:
- connectivity issues
- server behaviour
- DNS configurations
- access failures
Remote Host Identification
Searches may also occur when:
- firewall tools flag domains
- logs show unknown activity
- network scanners detect endpoints
Curiosity Around DynDNS Infrastructure
Many people are unfamiliar with Dynamic DNS systems, making unusual domain names appear suspicious even when used legitimately.
How Remote Access Systems Have Evolved
Remote networking has changed dramatically over the past decade.
Early Remote Networking
Older systems relied heavily on:
- manual IP tracking
- static configurations
- complicated networking setups
Cloud Connectivity Expansion
Modern systems increasingly integrate:
- cloud access
- mobile connectivity
- synchronised remote management
Smart-Home Infrastructure
IoT devices now commonly rely on:
- remote access
- cloud APIs
- internet-connected endpoints
This increased demand for simplified connectivity.
Hybrid Networking Environments
Today’s networking environments often combine:
- local infrastructure
- cloud services
- remote management systems
Dynamic DNS still plays a role in many of these setups.
Mysk2 Dyndns Org Mysk2 Switzerland vs Traditional Static Hosting
| Feature | Dynamic DNS Infrastructure | Traditional Static Hosting |
| IP flexibility | High | Lower |
| Home-network usage | Common | Rare |
| Remote accessibility | Strong | Moderate |
| Consumer networking relevance | High | Limited |
| Residential deployment | Frequent | Less common |
| Endpoint adaptability | Strong | Moderate |
This comparison highlights why Dynamic DNS remains useful for flexible networking.
Security Risks Associated With Remote Access Systems
Remote-access systems introduce important cybersecurity concerns.
Weak Passwords
Poor authentication remains one of the biggest risks.
Attackers frequently target:
- exposed login pages
- default credentials
- weak passwords
Open Ports
Improper router configuration may expose:
- vulnerable services
- insecure endpoints
- unnecessary access channels
to the public internet.
Malware Exposure
Unsecured systems may become vulnerable to:
- ransomware
- botnet activity
- unauthorised remote access
Unpatched Software
Outdated firmware and software create significant security risks.
Users should regularly update:
- routers
- NAS devices
- operating systems
- networking applications
How Cybercriminals Exploit Weak Remote Access Systems
This is an increasingly important cybersecurity topic.
Attackers commonly scan the internet for:
- exposed ports
- weak credentials
- outdated software
- vulnerable remote-access systems
Poorly secured Dynamic DNS endpoints may become targets because they remain consistently accessible through public domain names.
Common attack methods include:
- brute-force login attempts
- credential stuffing
- malware injection
- remote exploitation
This does not mean Dynamic DNS itself is unsafe.
The real issue is insecure configuration.
How to Secure Dynamic DNS and Remote Network Systems
Strong Authentication
Always use:
- unique passwords
- long credentials
- password managers
VPN Usage
VPNs improve security significantly by:
- encrypting traffic
- hiding exposed services
- reducing direct public access
Firewall Configuration
Proper firewall rules help:
- block unwanted traffic
- limit exposure
- monitor suspicious activity
Multi-Factor Authentication
MFA adds an additional protection layer beyond passwords.
This is increasingly recommended for:
- remote access
- NAS systems
- admin accounts
Software Updates
Regular updates reduce vulnerability exposure.
Users should monitor:
- firmware releases
- security patches
- networking software updates
Why Home Servers Use Dynamic DNS
Many home users now operate:
- media servers
- personal cloud systems
- backup infrastructure
- remote-access workstations
Dynamic DNS simplifies accessibility without requiring expensive static IP services.
This allows users to:
- remotely access files
- stream media
- manage home systems
- monitor cameras
from anywhere with internet connectivity.
Dynamic DNS vs Static IP Addresses
| Feature | Dynamic DNS | Static IP |
| Cost | Lower | Often higher |
| IP stability | Managed dynamically | Fixed |
| Residential usage | Common | Less common |
| Setup complexity | Moderate | Lower after setup |
| Flexibility | Strong | Moderate |
Both approaches have advantages depending on networking needs.
The Growing Importance of Home Networking in Switzerland
🇨🇭 Switzerland has seen increasing growth in:
- remote work
- smart-home adoption
- cloud connectivity
- personal networking infrastructure
Remote Work Expansion
Modern hybrid work environments require:
- secure remote connectivity
- reliable home networks
- remote-access systems
Smart-Home Systems
Connected devices now include:
- surveillance cameras
- smart lighting
- automation hubs
- media servers
Many rely on internet-accessible infrastructure.
NAS and Personal Cloud Growth
Users increasingly prefer:
- self-hosted storage
- personal backup systems
- privacy-focused file management
Dynamic DNS helps maintain access to these systems remotely.
Could Mysk2 Dyndns Org Be a Personal Server or NAS Endpoint?
This is technically possible.
Potential use cases may include:
- private NAS systems
- surveillance access
- remote desktop gateways
- file-sharing infrastructure
- hobby networking projects
However, without verified public ownership information, conclusions should remain cautious.
The domain should not automatically be assumed malicious or unsafe simply because it uses Dynamic DNS infrastructure.
How Search Engines Interpret Dynamic DNS Domains
Search engines treat Dynamic DNS domains differently from standard websites.
Limited Traditional Indexing
Many Dynamic DNS endpoints:
- are not public websites
- do not host standard content
- exist primarily for networking purposes
Security and Reputation Signals
Search systems may analyse:
- endpoint behaviour
- traffic patterns
- accessibility status
- security indicators
Technical vs Consumer Domains
Dynamic DNS domains are often more technical in nature than content-focused.
This changes:
- search behaviour
- indexing patterns
- ranking characteristics
The Future of Remote Networking and Dynamic DNS
Remote networking continues evolving rapidly.
IoT Expansion
More devices now require:
- persistent internet access
- remote monitoring
- cloud communication
AI-Powered Monitoring
AI systems increasingly help:
- detect intrusions
- monitor anomalies
- automate network diagnostics
Smart-Home Growth
Connected ecosystems continue expanding across:
- homes
- offices
- industrial environments
Decentralised Networking
Future networking trends may include:
- edge computing
- distributed infrastructure
- privacy-focused connectivity systems
Dynamic DNS may continue evolving alongside these technologies.
Best Practices for Securing Remote Network Access
Strong remote networking security depends on layered protection.
Recommended practices include:
- disabling unnecessary ports
- using VPN-only remote access
- enabling MFA
- monitoring login attempts
- regularly updating devices
- segmenting home networks
- avoiding default credentials
These measures significantly reduce risk exposure.
Frequently Asked Questions
What is mysk2.dyndns.org mysk2?
It appears to reference a Dynamic DNS-connected endpoint potentially associated with remote networking or home-server infrastructure.
What does Dynamic DNS do?
Dynamic DNS maps changing IP addresses to consistent domain names so systems remain remotely accessible.
Is DynDNS safe to use?
Dynamic DNS itself can be safe when properly configured with strong security measures.
Why do people use remote-access hosts?
Remote-access systems help users connect to:
- servers
- NAS devices
- surveillance systems
- workstations
from external locations.
How can Dynamic DNS systems be secured?
Security improves through:
- VPN usage
- strong passwords
- firewall protection
- MFA
- regular software updates
Final Thoughts on Mysk2 Dyndns Org Mysk2 Switzerland
Mysk2.dyndns.org mysk2 Switzerland reflects the growing role of Dynamic DNS infrastructure in enabling remote connectivity, home-network accessibility and internet-based system management across increasingly connected digital environments.
Rather than functioning like a traditional public website, Dynamic DNS domains often support:
- home servers
- NAS systems
- remote-access infrastructure
- smart-home connectivity
- networking flexibility
As remote work, IoT ecosystems and home networking continue expanding globally, Dynamic DNS technologies remain important tools for maintaining flexible internet accessibility.
At the same time, cybersecurity awareness is essential. Proper configuration, secure authentication and responsible remote-access practices play a major role in protecting internet-connected systems from modern threats.

