Cybersecurity Write for us
Cybersecurity Write for us is defending computers, servers, mobile devices, electronic systems, networks, and data from malicious attacks. It’s also known as data technology security or electronic information security.
What is Cyber Security?
Cyber security protects an organization and its employees and assets against cyber threats. As cyberattacks become more common and sophisticated and corporate networks grow more complex, various cyber security solutions require to mitigate corporate cyber risk.
The Different Types of Cybersecurity
Cyber security is a broad field covering several disciplines. It divides into seven main pillars:
- Network Security
- Cloud Security
- Endpoint Security
- Mobile Security
- IoT Security
- Application Security
- Zero Trust
Challenges of Cyber Security
An organization must coordinate its efforts through its information system for adequate cyber security.
Elements of cyber cover all of the following:
Network safety: Protecting the network from unwanted users, attacks, and intrusions.
Application security: Apps require endless updates and testing to protect these programs from attacks.
Endpoint security: Remote access is an essential part of the business but can also be a weak point for data. Endpoint safety is protecting remote access to a company’s network.
Data security: Inside networks and applications is data. Protecting company and client data is a separate layer of security. Identity management is a procedure for understanding every individual’s social access.
Database and infrastructure security: Everything in a network contains databases and physical equipment. Protecting these devices is similarly essential.
Cloud security: Many files are in digital environments or “the cloud.” Protecting data in a 100% online environment presents many tasks.
Security for mobile devices: Cell headphones and tablets contain almost every type of security challenge in and of themselves.
How to Submit Your Articles?
Before creating anything for our website, we ask that you carefully read our standards. Once your post complies with our requirements, you can email it to us at contact@techiestimes.com
Why Write for Techies Times – Cyber Security Write for Us
 Search Terms Connected to Cyber Security Write for Us
Search Terms Connected to Cyber Security Write for Us
- cyber security salary
- cyber security jobs
- cyber security certifications
- what is cyber security
- cyber security certification
- entry-level cyber security jobs
- cyber security degree
- cyber security course
- cyber security entry-level jobs
- cyber security analyst
- cyber security training
- cyber security companies
- cyber security analyst salary
- cyber security boot camp
- cyber security courses
- cyber security entry-level salary
- cyber security news
- online cyber security degree
- cyber security boot camp
- remote cyber security jobs
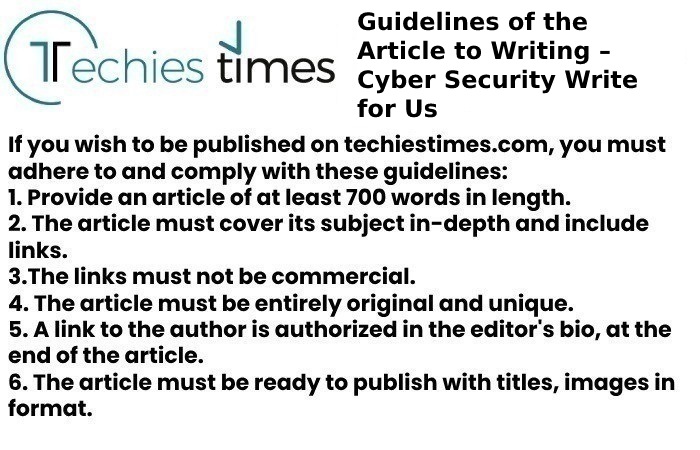
Guidelines of the Article to Writing – Cyber Security Write for Us
You can send your email to contact@techiestimes.com
Search Terms for Cyber Security Write for Us
- cyber security
- information security
- network security
- vulnerability
- penetration testing
- incident response
- threat intelligence
- malware
- ransomware
You can also try searching for terms related to specific types of cyber-attacks, such as:
- phishing
- spear phishing
- wi-fi hacking
- data breaches
- denial-of-service attacks
- zero-day attacks